
Securing blockchain systems and crypto assets has never become easier than with the Securosys Primus Blockchain HSM. Built on top either the Primus X-Series and E-Series general purpose HSM it brings additional unique functionality to the Distributed Ledger Technology (DLT). It provides multi-signature and multi-authorization functionality as well as blockchain algorithms and functions in a secure hardware platform. This allows the application (and its programmers) to focus on business functionality, while blockchain security and key access is managed by the Blockchain HSM.
The Securosys Primus Blockchain HSM is an extension of the FIPS certified Primus X-Series and E-Series HSM. Multi-signature and multi-authorization functionality is offered as the Smart Key Attributes (SKA) module. Different types of blockchain algorithms, like Bitcoin, Ethereum, Ripple, or IOTA can be loaded as independent modules.
Often, news reports are focused on the loss or theft of crypto assets worth millions of dollars. Making blockchain technology often a target to take the blame and being called out as not ripe enough for real use cases or their adoption. However, this is not a problem of the blockchain or distributed ledger technology. It can be avoided.
The weak link in the digital-currency system is the wallet, which is located on the application level and is used to manage the crypto assets. You can read more on this topic in our blog article on securing blockchain and crypto assets.
Secure generation and management of private keys, multi-signature access and use, targeted at financial institutions like banks, funds, exchanges and other blockchain systems
Key / Seed Generation
Side-channel protection
HW-based tamper response
Segregated functions in hardware and hardware “firewalls”
Cryptographic functions in hardware
Role model with multi factor authentication
Integrated key access control
HA redundancy and performance scalability
Smart Key Attributes (fine-granular access to individual keys)
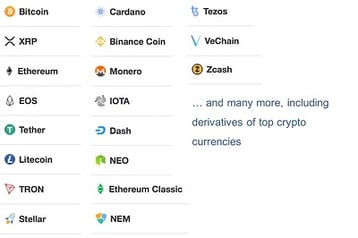
Support for various crypto currencies
Please find here our product overview or solutions overview page.